Regulations like GDPR are raising the bar for how companies handle data. If you're in a regulated industry, or making infrastructure decisions at the executive level, the question is increasingly not only whether your data is stored in Europe, but whether it's meaningfully outside the reach of foreign jurisdictions.
Simply choosing a data center in the right country doesn't make your organization sovereign. True sovereignty is both an architectural and a strategic decision, one that determines how your infrastructure is governed, who operates it, and what you're trading off for that control. Whether you're evaluating your cloud strategy or exploring options like the AWS European Sovereign Cloud (ESC), these dynamics matter.
The highlights of this article at a glance:
- A sovereign cloud goes beyond data residency – it enforces jurisdictional control, operational autonomy, and legal independence from foreign entities.
- The benefits are vast, but there are definite trade-offs – tighter control comes at the cost of scalability, speed of innovation, and increased operating expenses.
- Getting started with cloud sovereignty is more than a mere migration project – it’s a strategic decision that requires data classification, architecture alignment and regulatory expertise before anything is deployed.
- Sovereignty is rarely an all-or-nothing decision – most workloads don’t require sovereign environments, and applying it broadly can introduce unnecessary complexity and cost.
What is a sovereign cloud?
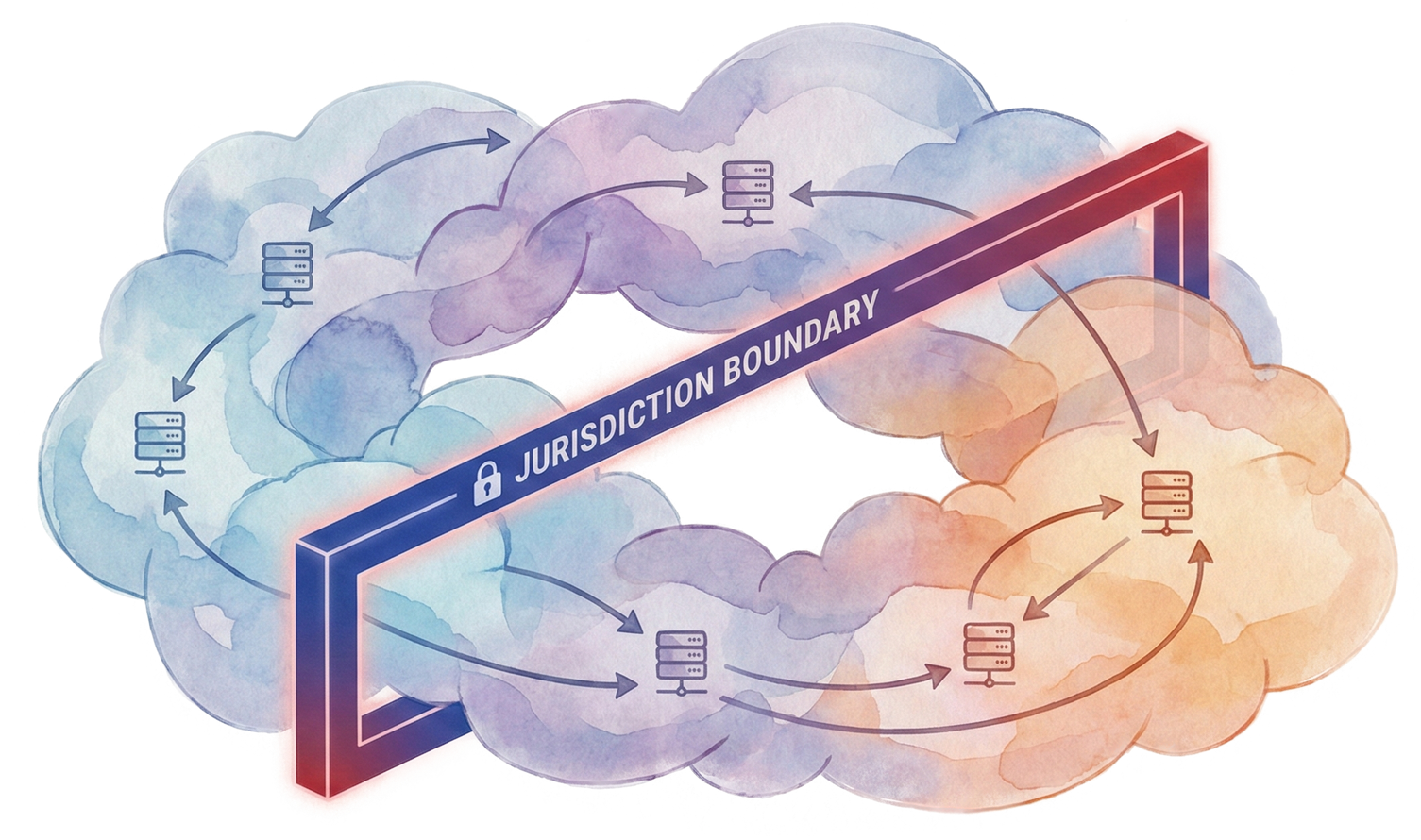
The sovereign cloud meaning goes beyond hosting data locally – it describes a cloud environment where data storage, processing, and operations are confined to a specific legal jurisdiction. It’s governed by local laws, operated by local personnel, and designed to reduce exposure to foreign legal access.
Sovereign cloud vs. private cloud – where the differences really matter
A private cloud provides a dedicated infrastructure and configuration control. A sovereign cloud adds jurisdictional governance, meaning data is not only isolated but legally bound to a specific region and operated under local laws and personnel controls, reducing foreign legal exposure.
Why cloud sovereignty matters – and why compliance is only the starting point
It's easy to treat digital sovereignty as a regulatory checkbox, but that undersells what's actually at stake. For companies handling sensitive data or operating in regulated industries, sovereignty is quickly becoming a strategic concern that touches resilience, trust, and long-term competitiveness.
Understanding the cloud sovereignty basics is important because companies often mistakenly reduce the concept to a vendor or product decision, when it’s really about governance and architecture. Regulations like GDPR don't just require data residency – they demand operational transparency, incident reporting, and auditability. A sovereign cloud is designed to address these requirements inherently, rather than treating them as an afterthought.
If you’re navigating sovereignty requirements and want a straight answer on what your architecture actually needs – not a framework, but a decision – that’s exactly what Intenics does.
Core capabilities of a sovereign cloud – and where the limits show
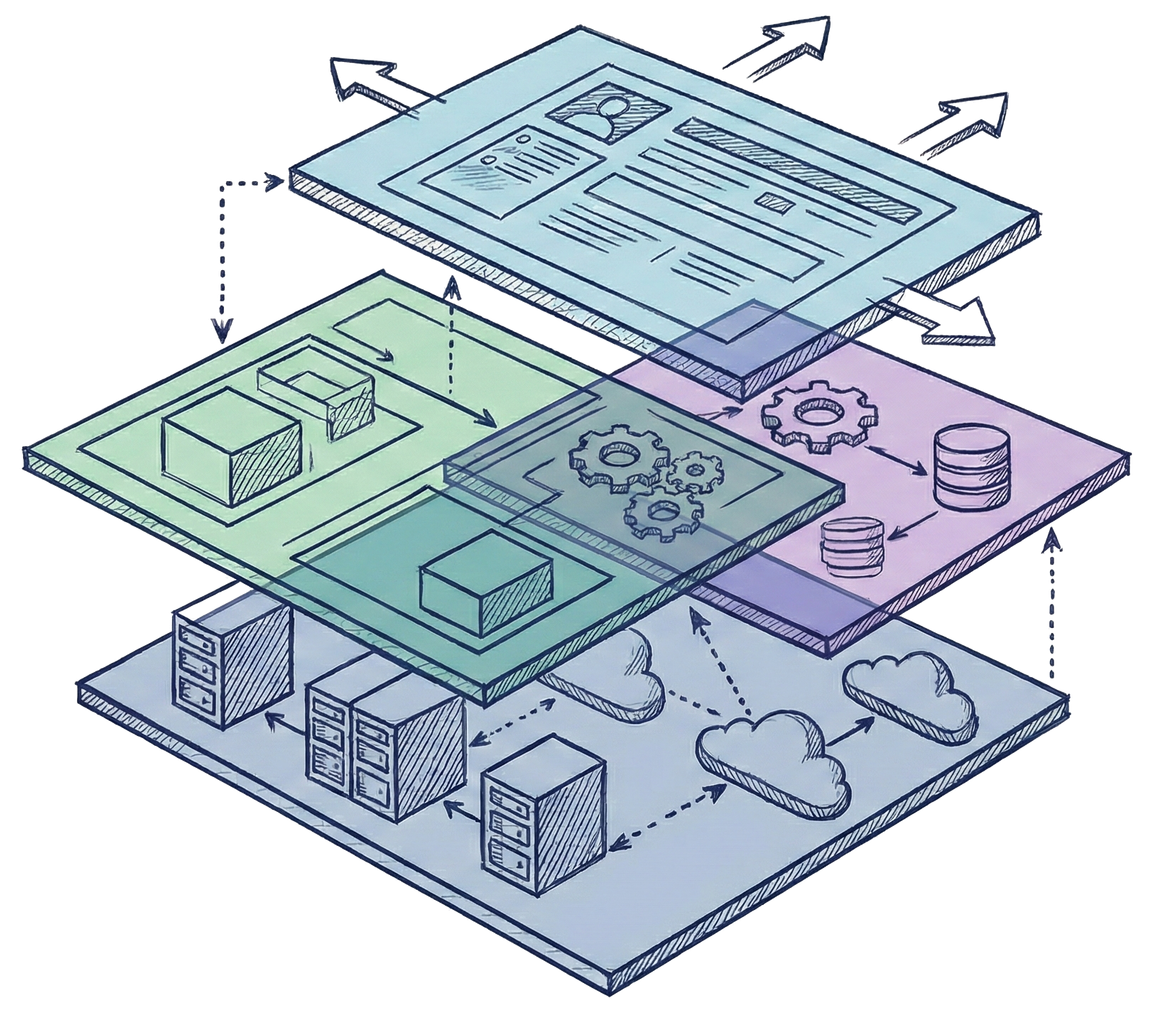
Sovereign cloud infrastructure is built around a set of capabilities that sets it apart from standard public or private deployments. Most sovereign cloud providers share four core pillars, with the AWS European Sovereign Cloud being a representative example of how each takes shape.
- Data residency and control: All data stays within a defined jurisdiction. Strict localization also concentrates geographical risk and may limit disaster recovery options.
- Operational autonomy: Infrastructure is run by local staff under local governance. The ESC is designed to operate with EU-based personnel, which means a smaller talent pool and potentially higher costs for round-the-clock coverage.
- Legal independence: Operations fall exclusively under local law. The ESC operates as a completely separate AWS partition, though the degree of legal independence ultimately depends on the contractual structure of your sovereign arrangement and how clearly operational boundaries are defined and enforced.
- Verifiability: Sovereignty must be auditable – transparent encryption, access logs, and external certification. This overhead may delay new feature rollouts.
Benefits of cloud sovereignty – and the trade-offs they imply
Sovereign cloud services deliver real advantages, but each one comes with a cost that should be considered carefully. When applied to the right workloads, these advantages can significantly improve control, compliance confidence, and long-term operational stability:
- Compliance by design: Data residency, privacy, and operational requirements are met out of the box, though compliance-first design can influence how services like serverless architecture are configured and deployed compared to standard global regions.
- Operational independence: Local staffing and governance reduce reliance on foreign entities, but can increase operating costs.
- Reduced foreign legal exposure: Local governance means your data is less likely to face foreign access requests, though in practice, exposure depends less on where data is stored and more on how access controls, contracts, and operational boundaries are actually implemented.
- Stronger security through isolation: Dedicated infrastructure and customer-managed encryption help prevent unauthorized access, but geographic isolation may conflict with cross-jurisdiction disaster recovery needs.

Key challenges companies face when pursuing cloud sovereignty
Pursuing cloud sovereignty shifts complexity rather than removing it. The following challenges highlight where increased control can introduce new technical and organizational trade-offs.
Control vs. scalability
The instinct to maximize control can backfire. Some regulated institutions in Europe have locked down their sovereign environments so tightly that platform upgrades stall, SaaS integration becomes impractical, and teams can't adopt new capabilities at speed. Autonomy taken to its extreme becomes isolation, and isolation can limit scalability. The challenge is architecting sovereignty in a way that there is still room to evolve.
Sovereignty vs. innovation speed
Sovereign environments sometimes lag behind global cloud regions. New AI tools, analytics services, and platform features land on global infrastructure first and reach sovereign partitions later. For companies that depend on cloud-native development practices to stay competitive, that's a genuine tension. Hybrid strategies can bridge the gap, but designing the boundary between sovereign and global environments takes architectural expertise, not just a vendor selection.
Data residency vs. resilience
Keeping data within a single jurisdiction satisfies regulatory requirements but concentrates risk. Global architectures offer redundancy and failover that sovereign models may lack, and companies often don't feel this tension until their sovereignty constraints and resilience goals collide in a disaster recovery plan.
What companies often underestimate when getting started with a sovereign cloud
The first step towards cloud sovereignty is not spinning up the infrastructure, it’s deciding what really needs to be sovereign. Most workloads don’t, but the ones involving regulated data, classified information, or business-critical intellectual property usually require sovereign-grade controls. Evaluating sovereign cloud solutions across the board, rather than only where sovereignty is genuinely required, is often unnecessary and inflates cost and complexity with little to no benefits.
The other big misstep is selecting a sovereign cloud platform and treating sovereignty as a mere migration project. Instead, companies should treat it as an architecture alignment challenge. Applications often have hidden dependencies on global cloud services that might break in a sovereign partition, and without the proper framework reviews and practices, companies may discover this at a moment when it’s very expensive to rectify.
The future of the sovereign cloud – and why waiting is the bigger risk
Sovereign cloud spending is forecast to hit $80 billion globally in 2026, with European investment growing by over 80% year over year. By 2027, Europe is expected to surpass North America in sovereign cloud IaaS spending (Gartner, 2026). The main drivers are structural: tightening regulations, geopolitical uncertainty, and the rise of AI workloads that often demand jurisdictional control.
This isn’t going to change anytime soon – sovereignty is increasingly moving from a niche requirement toward a baseline consideration. As the sovereign cloud moves from strategy into implementation, the real challenge is deciding where sovereignty creates value – and where it introduces constraints. Making these architectural trade-offs early is what prevents compliance goals from turning into long-term operational limitations.
Intenics helps teams cut through the complexity: We assess what sovereignty your workloads actually require, design the right architecture around it, and build it – hands-on, on AWS.






