As data governance frameworks tighten across Europe, organizations in regulated environments face a pointed question: can modern cloud infrastructure meet sovereignty requirements without becoming a compliance bottleneck – and without limiting long-term architectural flexibility?
The AWS European sovereign cloud (ESC) is AWS's structural answer to that question – a purpose-built cloud environment operating under a separate European legal and governance structure, designed from the ground up for the demands of European digital sovereignty, rather than an extension of existing AWS regions.
This article examines what makes the European sovereign cloud structurally different, where its real implications lie, and what organizations need to understand before treating it as a straightforward cloud option.
The highlights of this article at a glance:
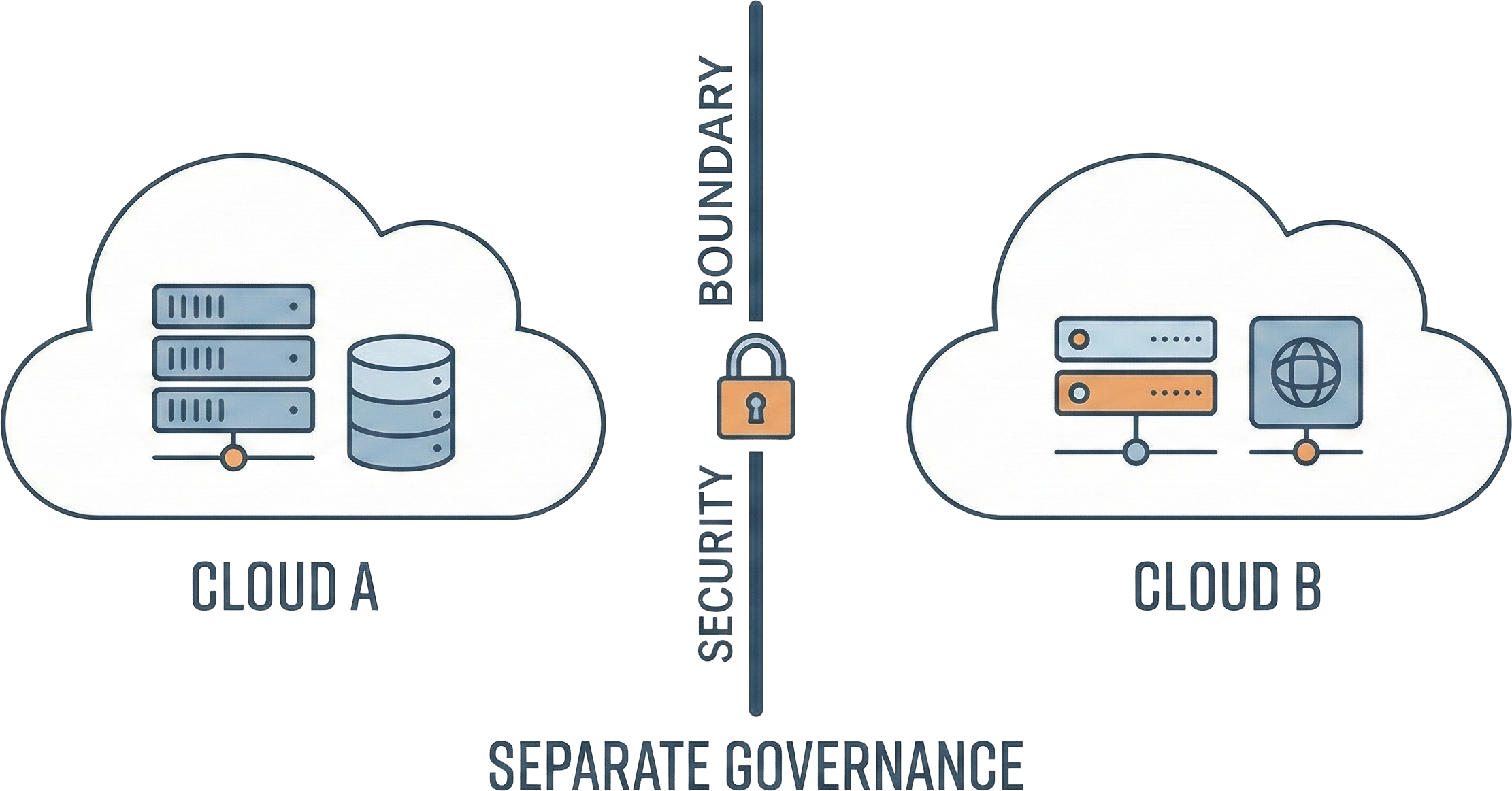
- The AWS European sovereign cloud (ESC) is not an extension of existing AWS infrastructure – it is a physically and logically separate environment with its own governance and legal entity.
- The relevance of the ESC is driven by regulatory and jurisdictional constraints, but its real impact is architectural – organizations must treat it as part of a broader multi-environment strategy rather than a standalone cloud option.
- A sovereign cloud does not automatically simplify compliance – it redistributes responsibility, making architectural readiness and governance maturity more critical than provider selection, even when the platform reduces jurisdictional exposure.
What is the AWS European sovereign cloud?
The AWS European sovereign cloud – sometimes also referred to as the Amazon European sovereign cloud – is an operationally independent cloud environment, now operational in Brandenburg, Germany, designed to meet European sovereignty and compliance requirements. Physically and logically separate from AWS’s global infrastructure, it operates under its own European governance structure while being staffed exclusively by EU citizens and designed to operate under European legal jurisdiction
Inside the AWS European sovereign cloud: structure and implications
The AWS European sovereign cloud is defined by structural properties that distinguish it from standard AWS regions, each introducing its own operational and governance implications for organizations operating within this environment.
- EU operational autonomy: All operations are performed exclusively by EU citizens residing in the EU. Operational support is handled within EU-based structures, requiring organizations to plan around a distinct operational and support model.
- Independent governance: The ESC operates under an AWS-owned German parent company governed by German and European law – a structurally different accountability and oversight framework requiring its own compliance and audit alignment.
- Isolated infrastructure: The ESC runs on its own hardware and network, including independent identity and access management systems, and EU-based root certificates – physically and logically separate from all other AWS regions, requiring clear separation strategies for connected workloads.
- Same performance and services: The ESC is not a scaled-down version of AWS. Instead, it is intended to deliver a comparable service portfolio, security and performance as existing AWS regions.
Why the European sovereign cloud matters beyond Europe
The relevance of the ESC doesn't stop at European borders. Discussions around sovereign cloud environments increasingly take place within a broader emerging EU sovereign cloud landscape, introducing architectural and strategic consequences that extend well beyond any single region.
- Global compliance pressure: Regulations like GDPR, NIS-2 and DORA are setting a precedent that other jurisdictions are beginning to follow. Organizations operating globally are increasingly required to demonstrate jurisdictional control over data not just in Europe, but in multiple markets simultaneously.
- Trust and reputational risk in regulated markets: In sectors where sensitive data is being handled, the ability to demonstrate data sovereignty is becoming a baseline expectation for market participation.
- Strategic diversification as an architectural option: For organizations that are already operating across multiple cloud environments, ESC introduces a sovereign deployment option that can be scoped to specific regions or regulatory requirements.
- Long-term readiness for sovereign environments: Organizations that develop strategies that work within sovereign environments now will be much better positioned as similar requirements emerge across other markets over time.
Architectural implications of a separate sovereign AWS environment
Deploying workloads in ESC is not a lift-and-shift exercise from existing AWS regions. The ESC’s structural separation introduces architectural considerations that affect how the broader cloud environment is designed and managed.
- The ESC operates as a separate AWS partition without native integration into global AWS environments, meaning organizations operating workloads in both environments need to treat this as a multi-environment architecture.
- Feature parity with global AWS services allows architectural decisions made for existing AWS workloads to be carried over without requiring redesigns around capability gaps.
- Modern architecture reduces friction, with organizations that have cloud-native development infrastructures built around serverless architecture, infrastructure-as-code and automation finding it much easier to scope, isolate and adapt workloads for the ESC.
Decision contexts where the ESC becomes relevant
In certain contexts, regulatory, legal, or organizational constraints can significantly narrow architectural alternatives, shifting the decision toward governance and compliance considerations rather than provider preference. The following scenarios illustrate where this shift typically occurs.
The public sector and governmental environments
Public authorities and government-adjacent organizations usually operate under national data protection mandates. The ESC comes with jurisdictional assurances and an EU-only staffing model that directly addresses many of these requirements.
Highly regulated industries with strict data residency requirements
Financial and healthcare organizations that handle sensitive data need to abide by regulatory frameworks that demand demonstrable control over data location and access, with the ESC addressing these demands at the core infrastructure level.
Multinational organizations balancing regional compliance
For organizations that operate globally, the ESC offers a sovereign environment that can be scoped to European operations without completely dismantling an organization’s broader cloud strategy.
Technology partners operating in sovereign contexts
Operating within the ESC allows independent software vendors and managed service providers to extend sovereignty capabilities to their customers by design, instead of relying solely on contractual guarantees.
Understanding these contexts is less about selecting a provider and more about assessing architectural readiness. If your organization operates in one of these contexts, Intenics can help you assess where the AWS European sovereign cloud fits into your architecture and compliance strategy.
What companies often underestimate about sovereign cloud adoption
A sovereign cloud does not reduce complexity – it redistributes it. At the same time, it can remove certain jurisdictional and operational constraints that regulated organizations cannot realistically mitigate through configuration alone. At the organizational level, things like data classification, access controls, audit trails, and compliance documentation don’t become easier inside a sovereign environment. They become explicit responsibilities organizations are expected to own. In this context, architecture readiness matters more than provider selection.

The European sovereign cloud as part of a broader cloud strategy
The ESC is an addition to existing cloud infrastructure, not a replacement. Most organizations that adopt ESC will continue running some of their workloads in other cloud environments, with the ESC scoped to workloads that have specific regulatory or jurisdictional requirements. Multi-environment strategies are becoming the norm, rather than the exception, and in this context, architectural consistency matters more than service parity.
The AWS European sovereign cloud as an architectural decision – not a default
The AWS European sovereign cloud is a structured and credible response to the growing demand for jurisdictional control over cloud infrastructure. However, alongside its sovereignty assurances, it also introduces new constraints that require deliberate architectural preparation – while at the same time enabling organizations to meet strict compliance requirements without abandoning modern cloud capability.
In practice, the real question is not whether the ESC is the right environment, but whether the organization is ready to operate within it effectively. In this situation, architectural experience and decision support matter most. As an AWS Advanced Consulting Partner, Intenics works with organizations at exactly that stage, helping them assess their readiness, navigate architectural decisions, and build towards a digitally sovereign environment with confidence.






